Long post about wireless hacking and security. Hopefully it will be of use for those that are interested. The "how" part is not a howto, but be limited to some facts. I will not give out the names and use of the tools, you are on your own for that.
Wireless hacking
Why?
Why would you want to secure wireless? Some already said "nobody will hack me, why would they?", "I'm not an interesting target", etc.
Here are some possibilities when your wireless is hacked:
- Your AP/internet could be abused for illegal things: sending spam, distributing child porn, sending email threats, etc etc.
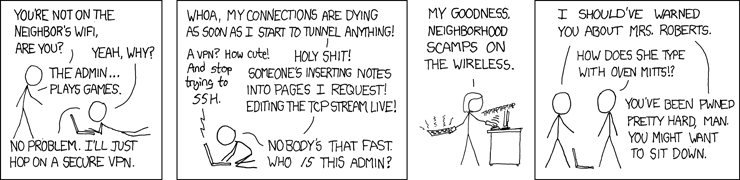
- Usernames & passwords could be stolen and then used/abused. (sites, email, ftp, etc) This attack is completely passive and thus you would never find out, until it's too late.
- Internet banking could go through an attacker instead of directly to the bank, giving them full access.
- Stealing bandwidth for up/downloads
- Pranks, like flipping all the images up-side down with surfing
In all those case your IP will show up, making you the suspect. While law enforcement _might_ find out you are indeed innocent, the hassle is hardly worth it, now is it? Especially when all your equipment is seized for an indefinite period.
Currently I'm investigating and writing a paper about this very issue.. if it's possible to find out if an AP is abused by someone else or not. This paper is partially for school and partially for the Dutch Forensic Institute (NFI).
I hope the "why" part is clear now.
How?
There are plenty of tools around, some tools are all round while others are specialized to attack specific kinds of measures/problems.
Mac filter can be easily bypassed by spoofing after sniffing.
Hidden SSID can easily be detected by sniffing.
Changing the ip range and/or switching DHCP off can easily be checked by sniffing.
Those 3 above options are not only useless, they make your own management a lot harder. If a friend comes over with a laptop or you buy a new laptop you need to do a bit of work to get internet on the new devices. Overall it's a hassle for you, not the (skilled) attacker.
WEP can be cracked through multiple ways.. time ranges from 3 to 15 minutes. If there is no data to capture/analyze then the AP can be forced to broadcast data.
WPA and WPA2 can cracked through dictionary bruteforce and/or rainbow tables. The rainbow tables are extremely fast although require a large amount of HD & Ram.
As sniffing is one of the first steps to do, a lot of the "security through obscurity" options are easily bypassed and shows that it's no security at all. Some tools even discover the "hidden" information automatically, helping out lesser skilled attackers.
Who?
Anyone who has the skill to do the "how" and is either curious or has any of the "why" motives/reasons.
Wireless Security
What?
What are the most secure options? Here is a list, starting with the strongest solution:
No wireless (sadly, this isn't always an option)
WPA2 + Radius (Best wireless security option, pretty much unbreakable with current techniques and hardware)
WPA + Radius
WPA2
WPA
WEP (To be honest, don't bother.. just a buy a new router if this is your only option)
SSID: Pick something fairly random, just make sure it's not in the top 1000 of SSID names. (Stuff like "wireless" or "linksys" is bad)
Passphrase: No matter what, where or how.. but _always_ pick a long and strong password/passphrase. In this case it means more than 20 characters and no dictionary or other common/normal words, not even medical or so. Just make it something (fairly) random using chars, numbers and special chars.
As doh pointed out you could lower the signalstrength so it is confined to your house and not covering half a block.
How?
Almost all of these options are fully dependant of your router, if your router doesn't support it you cant use it.
So make sure you buy proper stuff, although pretty much all wireless routers support WPA2 nowadays.
For Radius you need a server and of course support from the router. Not everyone has a server, so this might not be an option for everyone..
Long story short: Use WPA2 + RADIUS, if thats not an option use WPA2 with a proper passphrase.







 wifi profiles
wifi profiles 



